Can't add datasources from Rootservices? Setting the protocol for outbound ELM requests
OSLC connections depend on secure and consistent network connections. In many corporate IT systems, the standard minimum is changing to TLS 1.2. In most cases, our network connections will negotiate the highest supported TLS protocol. However, we have observed in some ELM deployments the outbound requests from ELM not automatically supporting TLS 1.2 for outbound requests and preventing connections to external applications.
There are two scenarios where we observe the behaviors of TLS mismatch.
When attempting to friend between an application and an OSLC Connect solution, we are notified of a protocol mismatch (either in the UI or in the logs).
When attempting to connect a TRS feed from LQE or LDX to OSLC Connect, we observe a “No data sources were found” with a valid rootservices URL. It will look similar to the following:
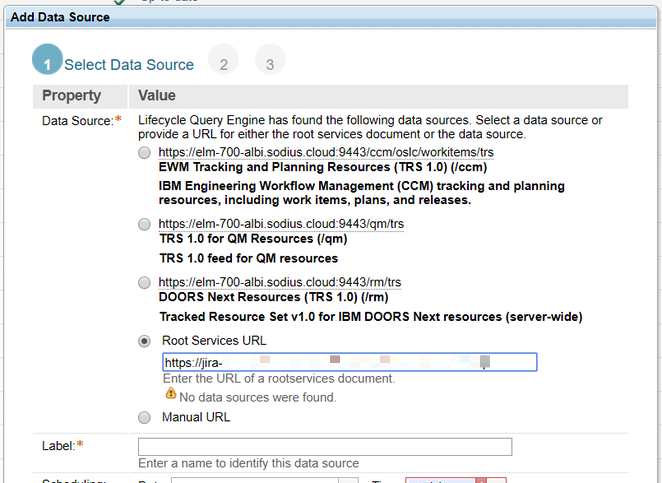
Once we have ruled out network connectivity issues (DNS, Firewall issues, bad rootservices URL), we have identified the protocol mismatch error. We can suggest the problem is that outbound requests for ELM are not supporting TLS 1.2.
We can validate this suggestion with the check of the Jira endpoint with a simple curl check as follows:
curl -IvL --tlsv1.2 https://myjiraserver/rest/oslc/1.0/rootservicesTo ensure ELM outbound requests support TLS 1.2, you should take the following steps for each application server with connection issues.
To perform the required actions demands both root access to the ELM application server(s) and performing a server restart. Please work with your ELM administrator to execute the following steps:
Navigate to your JazzTeamServer installation directory\server\liberty\servers\clm
Create or edit the file: jvm.options
Add the following line to this file:
CODE-Dcom.ibm.team.repository.transport.client.protocol=TLSv1.2Save the file and restart your ELM service.
Once everything is back up, verify that you are now able to make friend and TRS connections.